NanoCore Malware
Technical
details of NanoCore
Identification
Sample didn’t exist in virus total as shown in figure below.
The following table contains list of artifacts that had been analyzed
within this document.
|
PE timestamp |
SHA256 |
Size in bytes |
File name |
Description |
|
Thu Jun
25 03:38:24 2020 |
C0E3A49CBB496D4B77897BF1BBB7564391A37CEC |
200.00 KB (204800 bytes) |
Debug.exe |
dropper |
Summary
NanoCore is a Remote Access Trojan or RAT. This malware is highly
customizable with plugins which allow attackers to tailor its functionality to
their needs. Nanocore is created with the .NET framework which has a lot of
function to enable you steal any information to control current machine and
sent it to C&C server.
Important Note
The initialize stage of current sample (NanoCore
malware) is exactly the same code of malware njRAT.
Link
Code of NanoCore malware
Code of Nirjart malware
Technical
details
First Stage
It gets processes called SetDllDirectoryW and
SetDefaultDllDirectories as shown in figure
below.
It resolves
a lot of dll libraries as shown in figure below.
It gets
operating system version as shown in figure below.
It gets
information about any valid
installed or available code page as shown in figure below.
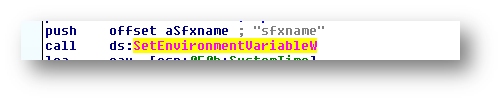
It sets new environment
variable called "sfxcmd" as shown in figure below.
It sets another
environment variable called "sfxpar" as shown in figure below.
It sets new variable
called "sfxname" as shown in figure below.
It gets
current date and time including minutes and seconds based on pattern as shown
in figure below.
It unlocks
resource called png as shown in figure below.
It control
current window using GetDC ,GetWindowLongW and GetWindow as shown in figures
below.
It creates
new file called __tmp_rar_sfx_access_check_ as
shown in figure with the following parameters as shown in table below.
|
hTemplateFile |
NULL |
|
dwFlagsAndAttributes |
NULL |
|
dwCreationDisposition |
CREATE_ALWAYS |
|
dwDesiredAccess |
GENERIC_READ_WRITE |
|
lpSecurityAttributes |
FILE_SHARE_READ |
|
dwShareMode |
GENERIC_READ_WRITE |
|
lpFileNam |
__tmp_rar_sfx_access_check_0 |
It map to
new file called winrarsfxmappingfile.tmp and run
it as shown in figure below.
Second stage
It creates new process called notepad.exe as shown in figure below.
|
PE timestamp |
Md5 |
Size in bytes |
Filename |
Description |
|
Sat Feb 21
16:49:37 2015
|
1993DF80C98372579FED41C32495BA5B |
207872 bytes |
notepad.exe |
RAT |
It connects to this domain called qwertyontop.ddns.net
as shown in figure below and it has full control of machine right now.
Some clear functions
It gets operating system version (major) and current domain as shown in
figure below.
It gets current username as shown in figure below.
All clear strings
- GetDetails
- ValidateSource
- ValidateBlock
- GetBlockHash
- WriteBlockData
- ReadBlockData
- HostDetails
- HostData
- Details
- SetThreadExecutionState
- GetCurrentProcess
- OpenProcess
- CloseHandle
- QueryDosDevice
- GetProcessImageFileName
- NtSetInformationProcess
- GetKernelObjectSecurity
- SetKernelObjectSecurity
- RegOpenKeyEx
- RegQueryValueEx
- RegCloseKey
- FindResourceEx
- LoadResource
- SizeofResource
- LockResource
- AllocConsole
- DeleteFile
- DnsQuery_A
- Variables
- ClientSettings
- BuilderSettings
- Connected
- #=qJEtGIBRUjtEusa67yMyqWQ==
- get_AddressFamily
- GetAddressBytes
- CreateInstance
- get_IsDisposed
- GetTypeFromHandle
- ContainsKey
- GetResourceString
- SetProjectError
- get_InnerException
- get_Message
- Remove
- Dispose
- GetObjectValue
- get_Count
- Dequeue
- Format
- ToArray
- GetEnumerator
- get_Current
- Contains
- ClearProjectError
- MoveNext
- VariableChanged
- ClientSettingChanged
- BuildingHostCache
- ConnectionFailed
- ConnectionStateChanged
- PipeClosed
- ReadPacket
- PluginUninstalling
- ClientUninstalling
- get_Item
- IsNullOrEmpty
- Write
- Close
- OpenRead
- get_Length
- get_Exists
- CompareString
- Empty
- set_Position
- Combine
- Change
- CheckForSyncLockOnValueType
- Enter
- set_Item
- get_Key
- get_Value
- Clear
- MaxValue
- add_ThreadException
- get_CurrentDomain
- add_UnhandledException
- add_AssemblyResolve
- get_StartupPath
- set_CurrentDirectory
- get_OSVersion
- get_Version
- get_Major
- Exists
- ReadAllBytes
- WriteAllBytes
- Compare
- GetFolderPath
- GetFiles
- GetFileNameWithoutExtension
- Enqueue
- ReadInt32
- ReadBytes
- GetExecutingAssembly
- op_Equality
- GetCustomAttributes
- ToByteArray
- GetBytes
- set_IV
- set_Key
- CreateDecryptor
- TransformFinalBlock
- set_AutoFlush
- Sleep
- get_ExecutablePath
- get_CurrentDirectory
- set_WorkingDirectory
- set_Verb
- Start
- get_UTF8
- GetString
- Replace
- Concat
- QueueUserWorkItem
- LocalMachine
- OpenSubKey
- ToInteger
- GetCurrent
- IsInRole
- ToUpper
- CreateDirectory
- get_UtcNow
- ToInt64
- FromBinary
- ToBinary
- ReadAllText
- WriteAllText
- TryParse
- EnterDebugMode
- LeaveDebugMode
- Increment
- Decrement
- GetTempFileName
- WaitForExit
- get_ExitCode
- Delete
- set_UseShellExecute
- set_CreateNoWindow
- set_WindowStyle
- GetDirectoryName
- CurrentUser
- DeleteValue
- get_ExceptionObject
- get_Exception
- ToLower
- get_Name
- StartsWith
- get_Now
- AddMinutes
- get_MachineName
- get_UserName
- get_StackTrace
- get_Day
- WriteLine
- ToLongDateString
- op_Subtraction
- get_TotalMilliseconds
- GetCallingAssembly
- get_Assembly
- GetName
- get_FullName
- GetPublicKeyToken
- AddRange
- get_Unicode
- GetFrame
- GetMethod
- get_DeclaringType
- get_MetadataToken
- GetManifestResourceStream
- Intern
- ReadByte
- BlockCopy
- get_Chars
- ToInt32
- get_InvokeRequired
- set_BlockSize
- CreateEncryptor
- GetType
- get_IsEnum
- GetUnderlyingType
- get_Width
- get_Height
- get_X
- get_Y
- SetLength
- ReadBoolean
- ReadChar
- ReadString
- ToCharArray
- ReadDecimal
- ReadDouble
- ReadInt64
- ReadSByte
- ReadInt16
- ReadSingle
- ReadUInt32
- ReadUInt64
- ReadUInt16
- get_Position
- GetConstructors
- GetParameters
- get_ParameterType
- GetInterfaces
- get_DiscretionaryAcl
- InsertAce
- get_BinaryLength
- GetBinaryForm
- AppendLine
- GetTypes
- IndexOf
- ComputeHash
- TransformBlock
- get_Hash
- NewGuid
- get_LocalEndPoint
- get_Port
- SetBuffer
- add_Completed
- GetHostEntry
- get_AddressList
- set_LingerState
- set_RemoteEndPoint
- ConnectAsync
- get_RemoteEndPoint
- ReceiveAsync
- get_SocketError
- get_LastOperation
- get_BytesTransferred
- get_Buffer
- Resize
- Collect
- get_Offset
- SendAsync
- PtrToStructure
- ToUInt32
- add_FormClosing
- add_Shown
- EnableVisualStyles
- set_ShowInTaskbar
- set_WindowState
- set_Visible
- MyTemplate
- 8.0.0.0
If you wanna learn malware analysis you can check my YouTube channel I'm trying publish analysis of malwares and some methods to analysis malwares.
Please don't forgot subscribe my channel Than you ♥
YouTube channel
https://www.youtube.com/channel/UCParXHaBXBmqRdHuVUg21pA
Reference
·
https://success.trendmicro.com/solution/1122912-nanocore-malware-information.
·
https://spanning.com/blog/nanocore-rat-malware-of-the-month/.























Comments
Post a Comment