Ransomware DearCry
Technical details of Ransomware
DearCry
Identification
|
Vendor |
Detection |
|
TrendMicro |
Ransom.Win32.DEARCRY.THCABBA |
|
McAfee |
Ransom-DearCry!CDDA3913408C |
|
Malwarebytes |
Ransom.DearCry |
The following table
contains list of artifacts that had been analyzed within this document.
Summary
DearCry is ransomware which encrypts files on a device and demands
ransom in exchange for decryption.
Technical
details
Anti-Analysis
It gets current system date and time as shown in figure below.
It starts new service called msupdate as
shown in figure below.
It generates key called “d37fc1eabc6783a418d23a8d2ba5db5a"
as shown in figure below. This hash will be note when ransoamware finished
encryption files.
It pushes two strings which related to communication with attack as
shown in figure below.
|
Email
address |
konedieyp@airmail.cc
or uenwonken@memail.com |
|
Message |
Your file has
been encrypted! |
It gets windows directory path (C:\Windows) as shown in figure below.
It will get paths of “Temp, APPDATA and PROGRAMFILES” then put paths in array as shown in
figure below.
It inserts hardcoded public key as shown in figure below.
Public key
MIIBCAKCAQEA5+mVBe75OvCzCW4oZHl7vqPwV2O4kgzgfp9odcL9LZc8Gy2+NJPDwrHbttKI3z4Yt3G04lX7bEp1RZjxUYfzX8qvaPC2EBduOjSN1WMSbJJrINs1IzkqXRrggJhSbp881Jr6NmpE6pns0Vfv//Hk1idHhxsXg6QKtfXlzAnRbgA1WepSDJq5H08WGFBZrgUVM0zBYI3JJH3b9jIRMVQMJUQ57w3jZpOnpFXSZoUy1YD7Y3Cu+n/Q6cEft6t29/FQgacXmeA2ajb7ssSbSntBpTpoyGc/kKoaihYPrHtNRhkMcZQayy5aXTgYtEjhzJAC+esXiTYqklWMXJS1EmUpoQIBAw==.
It resolves interesting strings which indicate the encryption process of
the target system's user files is implemented utilizing the OPENSSL library as
shown in figure below.
Interesting strings
crypto\evp\e_aes.c
crypto\bio\bio_lib.c
crypto\rsa\rsa_lib.c
crypto\evp\evp_enc.c
assertion failed: bl <= (int)sizeof(ctx->buf)
assertion failed: b <= sizeof ctx->buf
assertion failed: b <= sizeof ctx->final
assertion failed: EVP_CIPHER_CTX_iv_length(ctx) <=
(int)sizeof(ctx->iv)
assertion failed: ctx->cipher->block_size == 1 ||
ctx->cipher->block_size == 8 || ctx->cipher->block_size == 16
%lu:%s:%s:%d:%s
secure memory buffer
memory buffer
crypto\bio\bss_mem.c
CERTIFICATE REQUEST
NEW CERTIFICATE REQUEST
PKCS7
CERTIFICATE
RSA PUBLIC KEY
DH PARAMETERS
X9.42 DH PARAMETERS
crypto\rsa\rsa_crpt.c
crypto\evp\evp_lib.c
assertion failed: l <= sizeof(c->iv)
assertion failed: j <= sizeof(c->iv)
init fail
called a function that was disabled at compile-time
internal error
passed a null parameter
called a function you should not call
malloc failure
It gets logical drives as shown in figure below.
It gets drive type as shown in figure below.
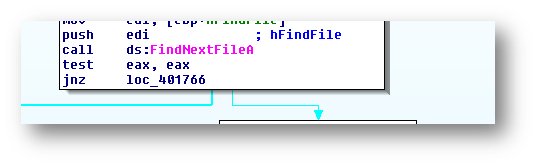
It searches for files in machine then start encryption using RSA as
shown in figure below.
Target files
It targets some extensions of files to encrypt them as shown in figure below.
After encryption end it delete malware service “msupdate” as shown in
figure below.
It adds extension called CRYPT as shown in figure2 below.
Encrypted
data
It writes the ransom note "readme.txt" to every folder as
shown in figure below.
Readme.txt
If you wanna learn malware analysis you can check my YouTube channel I'm trying publish analysis of malware and some methods to analysis malwares.
Please don't forgot subscribe my channel Than you ♥
YouTube channel
https://www.youtube.com/channel/UCParXHaBXBmqRdHuVUg21pA
Malware Analyst : Mahmoud El Menshawy
Contact me : mahmoudmorsy372@gmail.com
Linkedin:https://www.linkedin.com/in/mahmoudmorsy1/

















WpervorPnafu Mike Allen https://wakelet.com/wake/Ry4tzi1y45lsFGqI4tKNY
ReplyDeletetsonjalassco
hiefunPpist-i-Albuquerque Kim Romero https://www.shopdevenreaux.com/profile/rozaliarozaliavladymar/profile
ReplyDeletestochorileth
Operftehosmu1978 Dana Jones VMware Workstation
ReplyDeleteNulled
Avast Internet Security
nyatilimna
Mnabaron-dzu Tim Beard Software
ReplyDeletethere
quehattiber